In light of a new generic exploit for all LM32 version 7 based AMD SMUs (and possibly others) used in APUs
Discovered a new generic exploit for AMD SMUs based on LM32 version 7 that could be used in APUs and, most likely, GPUs as well. However it would not apply to Zen and SMU/RSMU CPUs, as they use Xtensa cores.
Rudolf Marek previously exploited a vulnerability in the LM32-based AMD SMU firmware, as discussed in his AMD x86 SMU firmware analysis talk .
However, it has been reported that AMD has allegedly patched the SMU message handler vulnerability.
The author mentions being lazy and not wanting to find a new exploit in the SMU firmware. However, he points out that he has developed a Ghidra LM32 plugin to analyze firmwares.
He wonders if there are other methods to run code in the SMU and mentions the ability to download the bootrom containing the HMAC key to sign custom firmwares and perform actions such as reading eFuse, gaining serial port access, and even reading/writing arbitrary DRAM.
Also, the existence of an unlocked region in the SRAM of the SMU for communication between the x86 world and the SMU is mentioned.
It is pointed out that the precise details are partly uncertain, such as the read lock value, but it is claimed that AMD has integrated the LM32 fully while retaining the debug functionality. Accesses occur via an indirect data/address scheme to the PCI root complex.
Finally, the author describes a series of steps for performing an exploit in the SMU. It is suggested to monitor the SRAM of the SMU to find a suitable space for the shellcode.
It mentions using a shellcode stub between the addresses 0x0003_F400and 0x0003_F600. Next, monitoring the SMU’s program counter is referenced through the SMC_PC_Cin register 0x80000370, generating a histogram to identify the address of the most executed instruction.
It also describes the steps for configuring registers SMC_LM32_DEBA, SMC_LM32_BP0and SMC_LM32_DCfor pointing to the debug vector table and enabling a hardware breakpoint.
It is suggested that you wait for the desired common instruction to execute in the firmware, at which time the breakpoint will be triggered and you will have access to the debug vector table shellcode.
It is stated that from within the SMU it is possible to disable the SRAM guards and read the bootrom.
The bootrom contains an encrypted HMAC key, but it mentions an eFuse bit that allows you to program a custom HMAC key. Finally, decompiling Ghidra from the bootrom of a Kaveri or Kabini APU is mentioned.
AUTH_START_ADDR = (FIRMWARE_HEADER_V7 *)(efuse_read1 & 0x7fffffff ); entry_point = (code *)AUTH_START_ADDR->EntryPoint; calc_digest[ 1 ] = 0xefcdab89 ; calc_digest[ 3 ] = 0x10325476 ; calc_digest[ 0 ] = 0x67452301 ; calc_digest[ 2 ] = 0x98badcfe ; // sha constant shit calc_digest[ 4 ] = 0xc3d2e1f0 ; do { efuse_read1 = read_volatile_4 (SMU_FIRMWARE_AUTH); // spin while SMU_KEY_RD_DONE != 11b } while ((efuse_read1 & 6 ) != 6 ); efuse_read1 = read_volatile_4(SMU_FIRMWARE_AUTH); // SMU_KEY_SEL if ((efuse_read1 & 0x20000 ) == 0 ) { key[ 0 ] = 0x3818c563 ; key[ 1 ] = 0x2f4383c1 ; key[ 2 ] = 0x21853a57 ; key[ 3 ] = 0xd7c7169 ; } else { key[ 0 ] = read_volatile_4 (SMU_SECURE_KEY_0); key[ 1 ] = read_volatile_4 (SMU_SECURE_KEY_1); key[ 2 ] = read_volatile_4 (SMU_SECURE_KEY_2); key[ 3 ] = read_volatile_4 (SMU_SECURE_KEY_3); } hmac (&AUTH_START_ADDR->Version,key,calc_digest,AUTH_START_ADDR->CodeSize >> 2 );
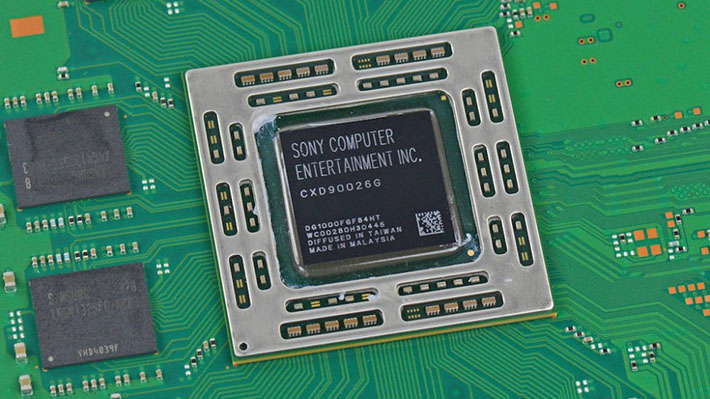
Generic exploit for LM32 version 7 based AMD SMUs could potentially impact PlayStation 4 consoles .
This exploit exploits vulnerabilities present in memory management and communication between the x86 world and the SMU, which may also be present in the APUs used by the PlayStation 4 console .
If the exploit is successfully applicable to such systems, it could allow privileged access to the SMU and open the possibility to perform unauthorized actions or change the functioning of the system.
However, it is important to note that actual applicability and impact on specific consoles require further evaluation and testing.
Download: Ghidra LM32 plugin
Source: github.com
